Silver fox phishing is a growing threat in India. Have you received an email that looks like it came from the Income Tax Department of India? If so, stop and think before you click anything. A dangerous Silver Fox phishing campaign is targeting Indian users with fake tax emails right now. The messages look very real. This Silver Fox phishing attack uses ValleyRAT malware to take over your system.
⚠️ Warning: If you have already clicked a suspicious tax email attachment, disconnect from the internet immediately and run a full antivirus scan.
In this post, I will explain what is happening. I will show how this attack works step by step. I will also cover who is at risk and what you can do right now to stay safe.
Silver Fox Phishing Key Takeaways
- Silver Fox is a Chinese hacking group targeting Indian users with phishing emails disguised as Income Tax Department notices.
- The attack uses ValleyRAT malware delivered through NSIS installers hidden in ZIP files to gain remote control of your system.
- DLL sideloading is the technical technique that allows the malware to execute without triggering traditional security alerts.
- Phishing attacks account for over 80 percent of reported security incidents worldwide, according to industry reports.
- Immediate actions include verifying sender domains, enabling multi-factor authentication, and reporting suspicious emails to CERT-In.

What Is the Silver Fox Phishing Attack?
Understanding Silver Fox Phishing and ValleyRAT
Silver Fox is a cybercrime group that security researchers believe operates out of China. In fact, they have been active since at least 2022, and their campaigns have targeted users across Asia, including China, Taiwan, Japan, Malaysia, and the Philippines. Moreover, in late 2025 and into 2026, they turned their sights on India.
The Silver Fox group has been active since at least 2022 and shows no signs of slowing down.
Their weapon of choice for this campaign is a piece of malware called ValleyRAT. RAT stands for Remote Access Trojan. In simple terms, once it gets onto your computer, the attacker can control your machine remotely. They can steal your files, log your keystrokes, and do pretty much anything they want without you knowing.
How Silver Fox Phishing Emails Work
Silver Fox makes its phishing emails look like real notices from India's Income Tax Department. The emails use strong language and official-looking formats. They also include PDF files that look like tax documents. It is a classic trick that plays on the fear and stress people feel during tax season.
How Does the Silver Fox Phishing Attack Work? Step-by-Step
Therefore, understanding how this attack works is important. It does not matter if you are a student, a working professional, or just someone who wants to stay safe online. Here is how the attack unfolds step by step.
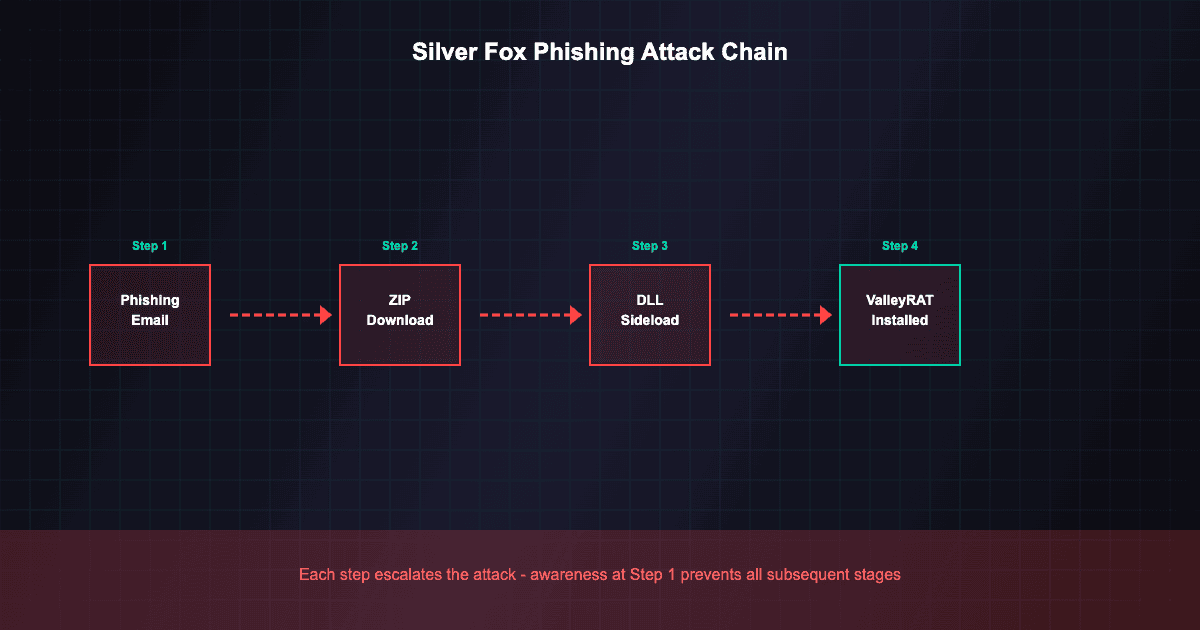
Silver Fox Phishing Step 1: The Email Arrives
You get an email that seems to come from the Income Tax Department. The subject line might say "Urgent: Tax Assessment Notice" or "Action Required: Income Tax Filing Issue." The email has a PDF file or a link to download a ZIP file named "tax affairs.zip."
Step 2: You Open the Attachment
When you open the PDF or click the link, the email redirects you to a domain the attackers control. This site has a ZIP file that looks like a real tax document. But the ZIP hides an NSIS installer. This is a type of setup tool often used for Windows apps.
Step 3: DLL Sideloading Begins
Next, the installer drops a legitimate signed program file, often a popular app like Thunder.exe. It also places a harmful DLL file alongside it. When the real program runs, it loads the harmful DLL automatically. This happens because of a trick called DLL search order hijacking. In short, the system looks for DLL files in a set order. The attackers place their harmful DLL where the system finds it first.
DLL sideloading is a sneaky trick that helps attackers slip past your security tools without getting caught.
Step 4: ValleyRAT Gets Installed
As a result, once the harmful DLL runs, it installs ValleyRAT on your system. This trojan then changes your Windows registry so it starts every time you boot your computer. From this point on, the attacker has a backdoor into your machine.
Step 5: The Attacker Takes Control
Consequently, with ValleyRAT active, the attacker can now log your keystrokes to steal passwords. They can also run commands on your machine, move files back and forth, take screenshots, and watch your activity in real time. Meanwhile, all of this happens silently in the background while you go about your normal work.
Why Is Silver Fox Phishing Particularly Dangerous for Indians?
Silver Fox Phishing Exploits Tax Season as an Attack Vector
Tax season is stressful for everyone. This makes Silver Fox phishing emails very effective. When people see an email from the Income Tax Department, they want to open it right away. They do not stop to check if it is real. Silver Fox knows this and uses it to their advantage.
Expansion of Digital Infrastructure and Growing Attack Surface
Additionally, India is going through a massive digital shift. More people file taxes online than ever before. More businesses use digital workflows. As a result, the overall attack surface has grown a lot. A Gartner report from March 2026 says India will spend 3.4 billion dollars on security this year. That shows how serious the threat has become.
Regular users and small business owners do not have the same strong security that big companies use.
However, here is the problem. Most of that spending happens at big companies. Individual users, freelancers, small business owners, and students often lack the same level of safety. In other words, those are exactly the people Silver Fox targets with these tax-themed lures.
Who Is Behind Silver Fox Phishing and What Do They Want?
Operations and Motivations
The Silver Fox phishing group is not new. Researchers have tracked them since 2022, and their goals are varied. Unlike some hackers who only spy or only steal money, Silver Fox does both.
RATs like ValleyRAT are now the top malware tool used in targeted attacks across Asia.
For example, their operations include spying on companies, stealing money, mining crypto, disrupting target groups, and collecting data for future attacks. As a result, this makes them hard to predict and very dangerous. For instance, when they break into a system, they might use it for spying today and crypto mining tomorrow.
Geographic Expansion and Scaling Activities
Furthermore, researchers have mapped Silver Fox phishing tactics using the MITRE ATT&CK framework. Their earlier campaigns hit users in China and Taiwan. However, the move into India, Japan, Malaysia, Thailand, and other parts of South and Southeast Asia shows they are growing fast. CERT-In reports show that India saw a 45% rise in malware attacks in 2025 compared to the year before.
How to Protect Yourself from Silver Fox Phishing Attacks
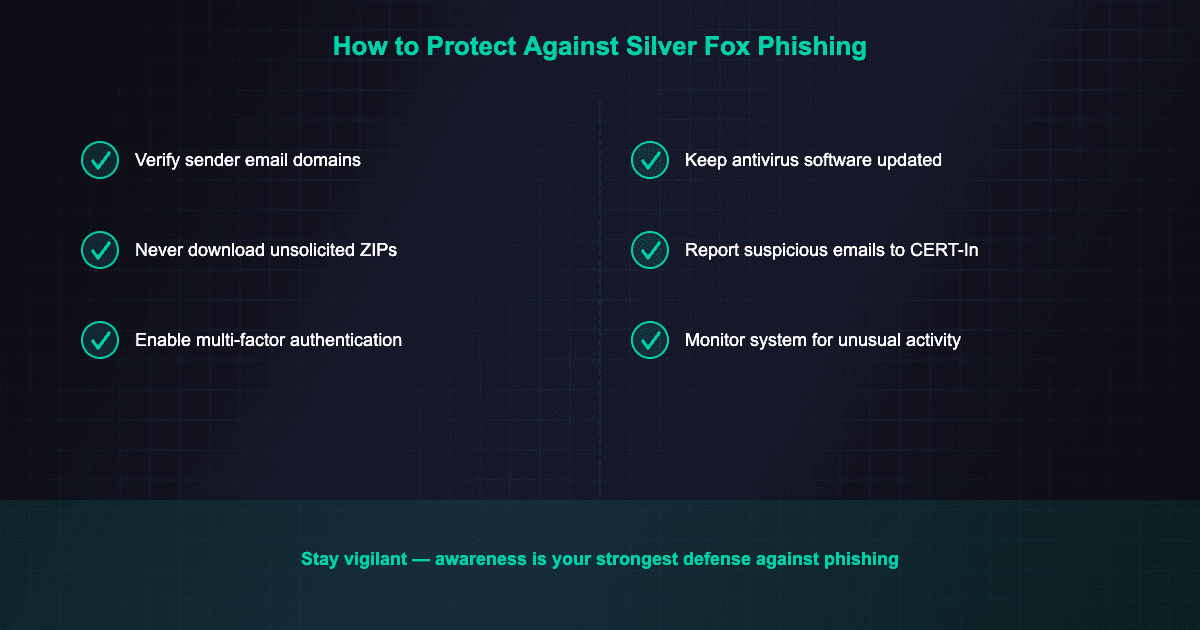
Whether you work in cybersecurity or just use the internet daily, there are simple steps you can take right now. These will help you stay safe from Silver Fox phishing attacks.
1. Never Trust Tax Emails Blindly
The Income Tax Department will never send you an email asking you to download a ZIP file out of the blue. If you get such an email, do not click any links. Do not download any files. Go directly to the official Income Tax portal at incometax.gov.in and log in to check for any genuine notices.
💡 Pro Tip: Bookmark the official Income Tax portal so you always have quick access to the real site.
2. Check the Sender's Email Address
Phishing emails often come from addresses that look close to real ones but have small changes. So look at the domain name with care. If it does not end in gov.in, it is most likely fake.
3. Keep Your Antivirus Updated
Make sure you install a reputable antivirus solution and keep it updated to the latest version. Most modern antivirus tools can spot and block NSIS installers and known RAT files. Windows Defender, which comes with Windows 10 and 11, has also gotten much better. It can catch many of these threats automatically.
💡 Pro Tip: Want to build your skills? Try our free cybersecurity labs. You can practice finding malware and learning attack chains in a safe space.
4. Enable Multi-Factor Authentication Everywhere
However, even if your credentials get stolen through a keylogger, multi-factor authentication adds an extra layer of safety. Turn it on for your email, bank, tax filing, and other key accounts.
5. Monitor Your System for Unusual Activity
For instance, if your computer suddenly becomes slow, your hard drive is very active, or you see odd processes in Task Manager, these could be signs of a RAT infection. In that case, run a full system scan right away. Also, seek help from a professional if you are not sure what to do.
6. Report Suspicious Emails
If you get a suspicious Silver Fox phishing email that claims to be from the Income Tax Department, report it to CERT-In. This is India's Computer Emergency Response Team. Your report helps them track these attacks and warn others.
What Should Organisations Do About Silver Fox Phishing?
Employee Training and Email Security
If you are an IT admin or security professional at an Indian company, there are extra steps you should take to keep your users safe.
First, run Silver Fox phishing awareness training that focuses on tax-themed lures. Make sure your team knows what to look for and whom to report odd emails to. Second, set up email filters that flag or block emails with ZIP files from outside senders, especially during tax season.
Advanced Detection and Threat Intelligence
In addition, organizations should consider hiring trained SOC professionals to monitor for threats. Our guide on how to become a SOC analyst in India covers the skills needed for this role.
Third, use Endpoint Detection and Response (EDR) tools that can spot DLL sideloading tricks and odd process activity. Fourth, watch your network for links to known Silver Fox command and control servers. Threat intelligence feeds from providers like CloudSEK and Sekoia can help with this.
Companies that use a zero trust security model do much better at stopping phishing attacks like those from Silver Fox.
Silver Fox Phishing and India's Growing Cyber Threat Landscape
Rising Threat Vectors and Emerging Attack Types
In fact, the Silver Fox campaign is not a one-off event. India's cyber threat scene has become one of the most active in the world. For example, state-backed attacks, ransomware, deepfake fraud, and hacktivism are all on the rise. In fact, AI deepfake fraud alone cost India about 70,000 crore rupees in 2025.
Regulatory Response and Individual Responsibility
Of course, the launch of the DPDP Act and the Data Protection Board in late 2025 are good steps. However, rules alone cannot stop phishing emails from reaching your inbox. In the end, that duty falls on each one of us as individuals, as professionals, and as groups.
As threats grow and change, you must keep learning about new attack methods. This is key for anyone who works in tech.
Moreover, getting the right certifications can accelerate your cybersecurity career. See our list of best IT certifications for beginners to find the right starting point.
If you are a cybersecurity student or just starting your security career, study campaigns like Silver Fox phishing closely. Learn how the attack chain works. Study the social tricks and the tech behind DLL sideloading and RATs. This will give you skills that go far beyond what any textbook can teach. Consider exploring our cybersecurity career roadmap to guide your learning path.
Silver Fox Phishing: Frequently Asked Questions
Silver Fox Phishing: Final Thoughts
Stay Alert and Verify Before Acting
In conclusion, the Silver Fox phishing campaign in India is a clear reminder that cyber threats do not pick sides. Whether you are a big company or a college student filing your first tax return, you are a target. Above all, the best defence is awareness. Now that you know how this attack works, you are already better prepared than most.
Continuous Learning for Cybersecurity Professionals
So stay alert, verify before you click, and keep learning. That is how we stay one step ahead. In particular, real-world campaigns like Silver Fox teach us more about modern attacks than any course. By learning about these threats, you not only protect yourself but also grow as a cybersecurity professional.
About the Author
Written by Bhanu Prakash, founder of ElevateWithB. Bhanu writes about cybersecurity, cloud computing, and tech careers to help students and professionals stay ahead in the Indian tech industry.
Disclaimer: This article was written with the assistance of AI tools for research, structuring, and drafting. All facts, recommendations, and opinions have been reviewed and verified by the author to ensure accuracy and reliability.